Introduction: The Growing Need for Cybersecurity
Have you ever thought about the security of your digital life and assets? Who is guarding your data, and could it be at risk? Therefore, this introduction to cybersecurity shows why protecting your digital world is more important than ever.
Many people hear about these incidents in the news. They assume these problems affect only large companies or technical experts. But the truth is alarming. Anyone connected to the digital world can become a target.
Therefore, understanding cybersecurity and its mechanisms is becoming more crucial. An introduction to cybersecurity is not just about technical complexity. It involves understanding how the digital landscape works. It also covers how threats start and how to prevent them.
For people interested in technology and online safety, this knowledge is a key first step. It also helps you stay up to date in a changing digital world. It builds awareness and opens new opportunities.
What Is Cybersecurity? A Beginner-Friendly Explanation.
According to Cisco; ‘Cybersecurity is the practice of protecting systems, networks, and programs from digital attacks. These cyberattacks are usually aimed at accessing, changing, or destroying sensitive information; extorting money from users through ransomware; or interrupting normal business processes.’
National Cyber Security Centre UK (NCSC) expresses that ‘Cybersecurity helps individuals and organizations reduce the risk and impact of cyber-attacks.’
Cybersecurity isn’t just about complex code. It’s the digital wall protecting our banking, healthcare, and private conversations. To understand rapid changes, we must examine how the digital landscape has evolved recently.
The Digital Shift: 2020 vs. 2026
| Feature | 2020 (The Past) | 2026 (The Present) |
| Personal Data | Stored mostly in physical files or basic clouds. | Everything, from health to finances, is on the cloud. |
| Cyber Threats | Basic viruses and “spam” emails. | AI-powered attacks and global ransomware. |
| Job Market | A “good-to-have” skill for IT staff. | A ‘boardroom-level’ priority with zero percent unemployment for skilled specialists. |
| Security Status | Reactive (Fixing it after it breaks). | Proactive (Preventing it before it happens). |
Table 1: A Comparison between past & present practices
In short, cybersecurity is the collective effort to safeguard digital systems, networks, and data. It also ensures users’ safety from malicious online activities. It involves deploying technologies, processes, and policies to protect infrastructure from cyberattacks.
The Modern Cyber Threat Landscape
The digital world is expanding and increasingly dangerous. Attackers exploit vulnerabilities in networks, software, and human behaviour to steal data and cause disruption. Modern security training is vital to address this hidden war’s four main fronts.
- Ransomware:
- Phishing:
- Data Breaches:
- Identity Theft
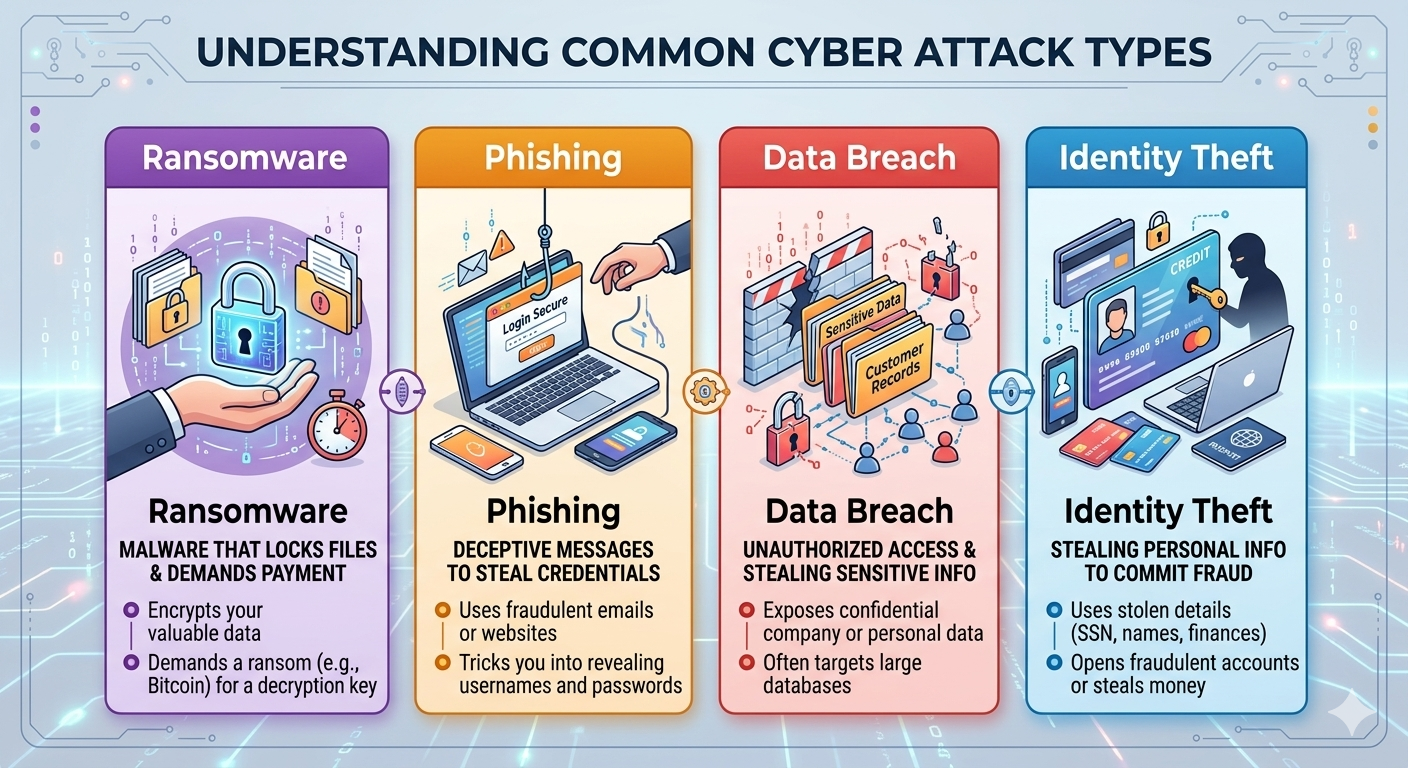
The author’s illustration is based on cyberattack types
This isn’t merely theoretical. Data shows a disturbing trend. As global connectivity grows, cybercriminal profit opportunities rapidly increase.
Look at the annual cost of global cybercrime.
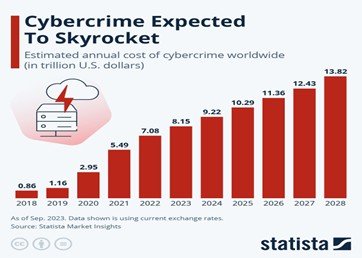
The financial impact of cyberattacks continues to rise. It is affecting organizations, governments, and individuals worldwide.
Several global research organizations regularly analyse the economic impact of cybercrime and the growing risks it poses.
Reports from Cybercrime Report by Cybersecurity Ventures show that cybercrime costs are rising fast worldwide.
The World Economic Forum analysis of global cybercrime reports the same trend. Academic cybersecurity research also supports this finding.
Their analysis shows how cyber threats have evolved into a major global economic challenge.
Real-World Cyberattack Examples
No country is immune to cyberattacks. Attackers are adapting to new technology. It sometimes becomes difficult for governments to defend themselves. Vulnerability remains high for both individuals and organizations. The major rising crime is impersonation.
Recently, an article was published in the BBC on Feb 26th,2026.
The report states that attackers ran a Facebook ad impersonating a Government Investment Platform.
They used images of politicians and official logos to look legitimate.
Here are some of the cyberattack cases that affected the world on a massive level.
WannaCry ransomware attack (2017)
It spread to over 150 countries by exploiting a vulnerability in Microsoft Windows. It encrypted files and demanded cryptocurrency ransoms, disrupting hospitals and businesses worldwide.
Equifax data breach (2017)
It happened when attackers used an unpatched flaw in a web app. This exposed the personal data of nearly 147 million people. This is still one of the largest breaches in history. It highlights the dangers of weak vulnerability management.
Colonial Pipeline ransomware attack (2021)
The target was one of the largest fuel pipeline operators in the United States. The company briefly shut down pipeline operations after the attack damaged internal systems. This caused fuel shortages and supply disruptions in several states.
Indian Council of Medical Research ICMR (2023)
Data from about 815 million Indian citizens was stolen from a COVID-19 testing database. It was sold on the dark web. It included passport numbers and addresses, marking a massive health data breach.
Russian hijacking of Pakistani hacking group infrastructure: (2024)
In December 2024, Russian hackers took control of systems used by a Pakistani group. They used them to view sensitive data from South Asian government and military targets.
These incidents show that cyberattacks cause extensive damage, ranging from financial loss to infrastructure disruption. They highlight the urgent need for robust cybersecurity measures across all sectors.
Core Principles of Cybersecurity
A set of fundamental principles guides cybersecurity. They help protect digital systems and information from unauthorised access and cyber threats.
One of the most widely recognized frameworks is the CIA triad. It consists of three essential components:
- Confidentiality
- Integrity
- Availability
These principles form the foundation of many cybersecurity strategies. They safeguard data and maintain secure digital environments. 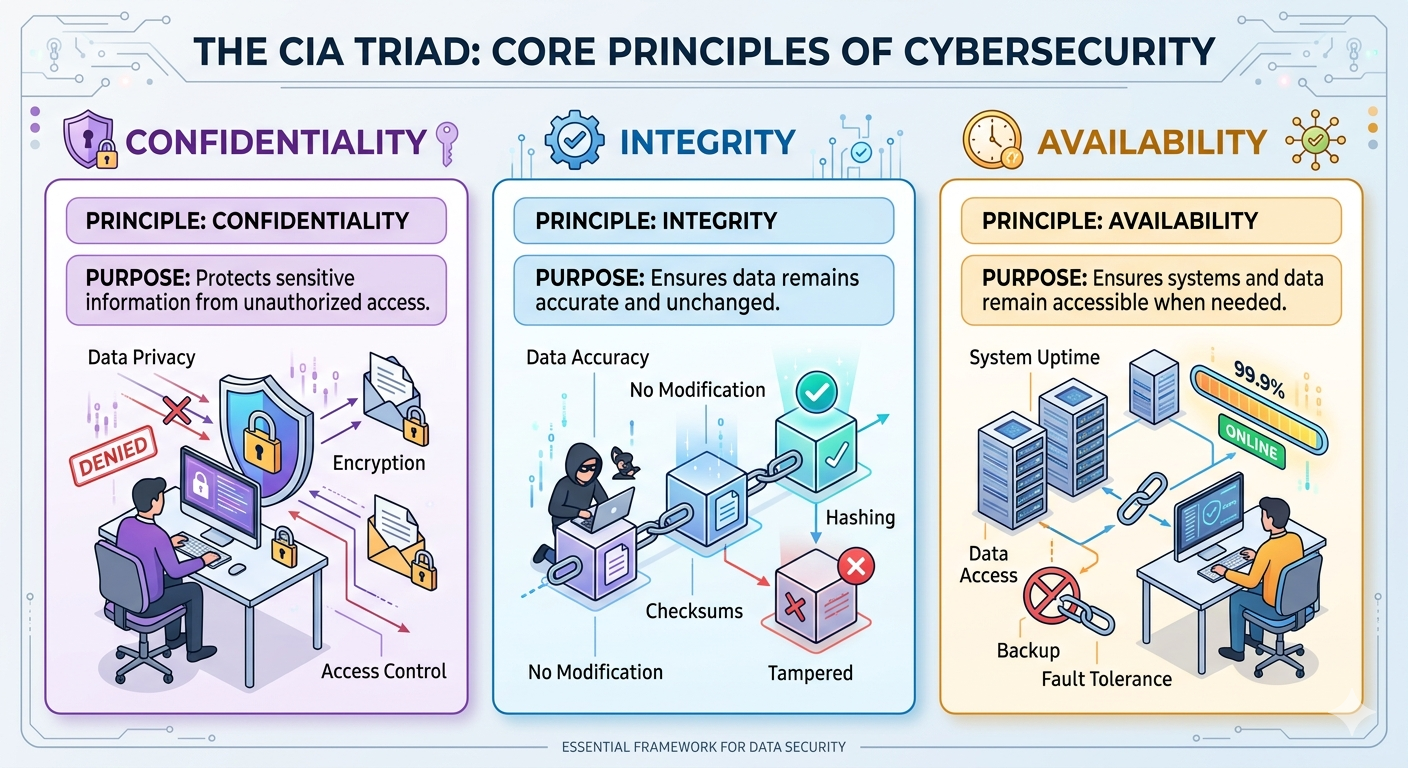 The author’s illustration is based on cybersecurity principles.
The author’s illustration is based on cybersecurity principles.
Together, these principles guide organizations in developing effective security practices. They also help in maintaining the stability and reliability of their digital infrastructure.
The Digital Elite: Mastering the Skills of 2026
In a world where a data breach can bankrupt a billion-dollar company. Those who stop them are not just IT staff. They are vital assets. To join this group, you require more than a degree. You require a specific, high-impact toolkit.
The “Must-Have” Skills for the Modern Guardian
- AI-driven Threat Detection
- Cloud Defence Architecture
- Ethical Hacking
- Strategic Risk Communication
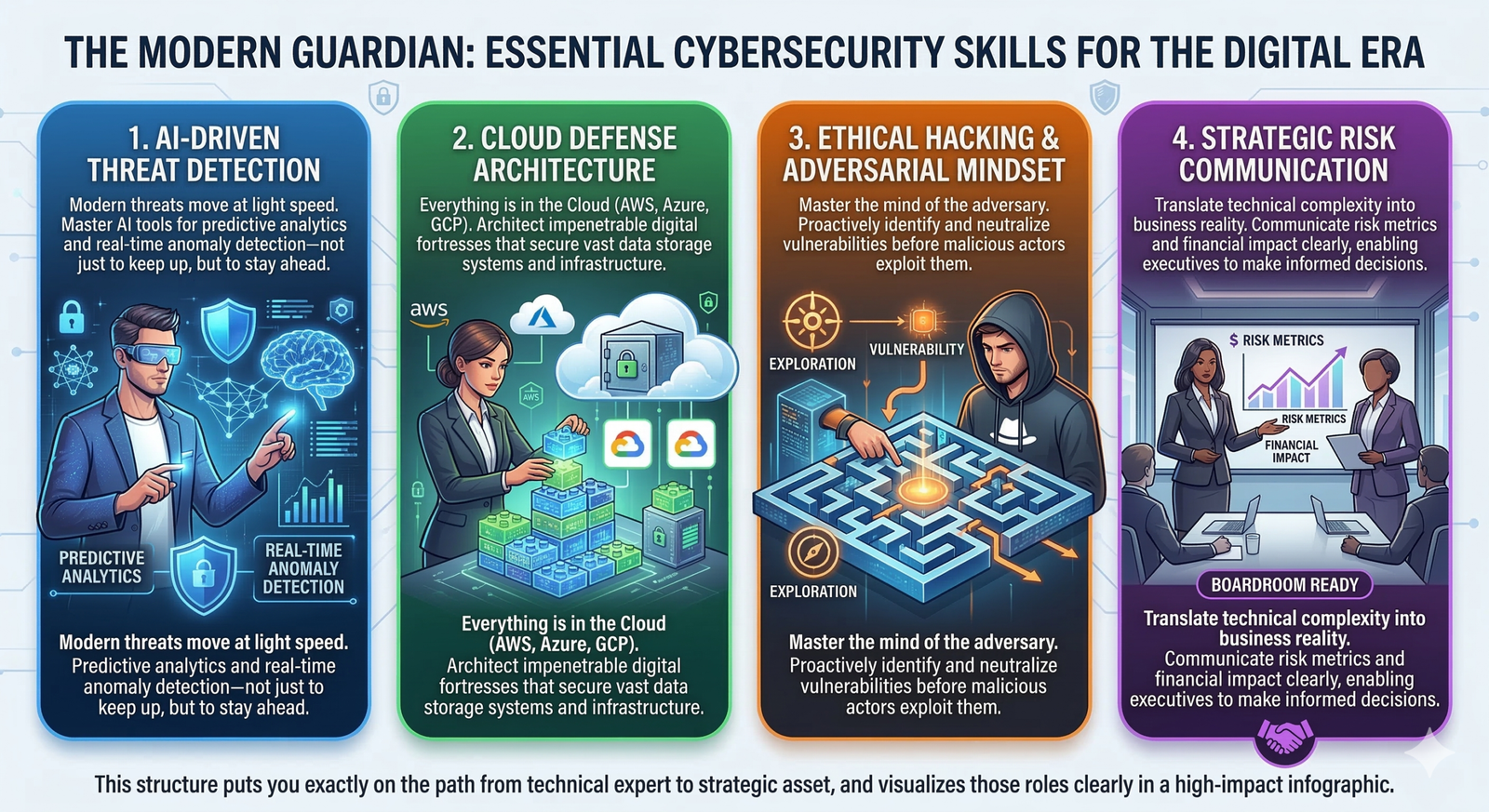
Essential Cybersecurity Skills for the Digital Era
The Industry Reality: Demand vs. Supply
Talent Gap: Millions of cybersecurity jobs are unfilled worldwide. Many businesses cannot find people with the right hands-on training.
Why does this matter to you? When demand is high and supply is low, you don’t just get a job; instead, you gain leverage. You can choose your remote-work balance, your benefits, and your pathway.
How can you close the gap? Many people try to learn cybersecurity through random YouTube videos, but in such a critical field, guessing isn’t enough. A structured, guided approach helps you learn faster. What usually takes years can be achieved in months.
Bridging the Skills Gap in Cybersecurity
While the demand for cybersecurity professionals continues to grow, many learners struggle to turn knowledge into real-world skills. The gap between theory and practical expertise often slows progress.
This is where structured, hands-on training makes a difference. A guided learning environment helps build job-ready skills faster and with clarity.
A Practical Learning Approach
One such institution in Gujrat, “Adan Institute of Technology”, focuses on practical, industry-relevant training. Its programs prepare students for modern cybersecurity challenges and help them become job-ready within months.
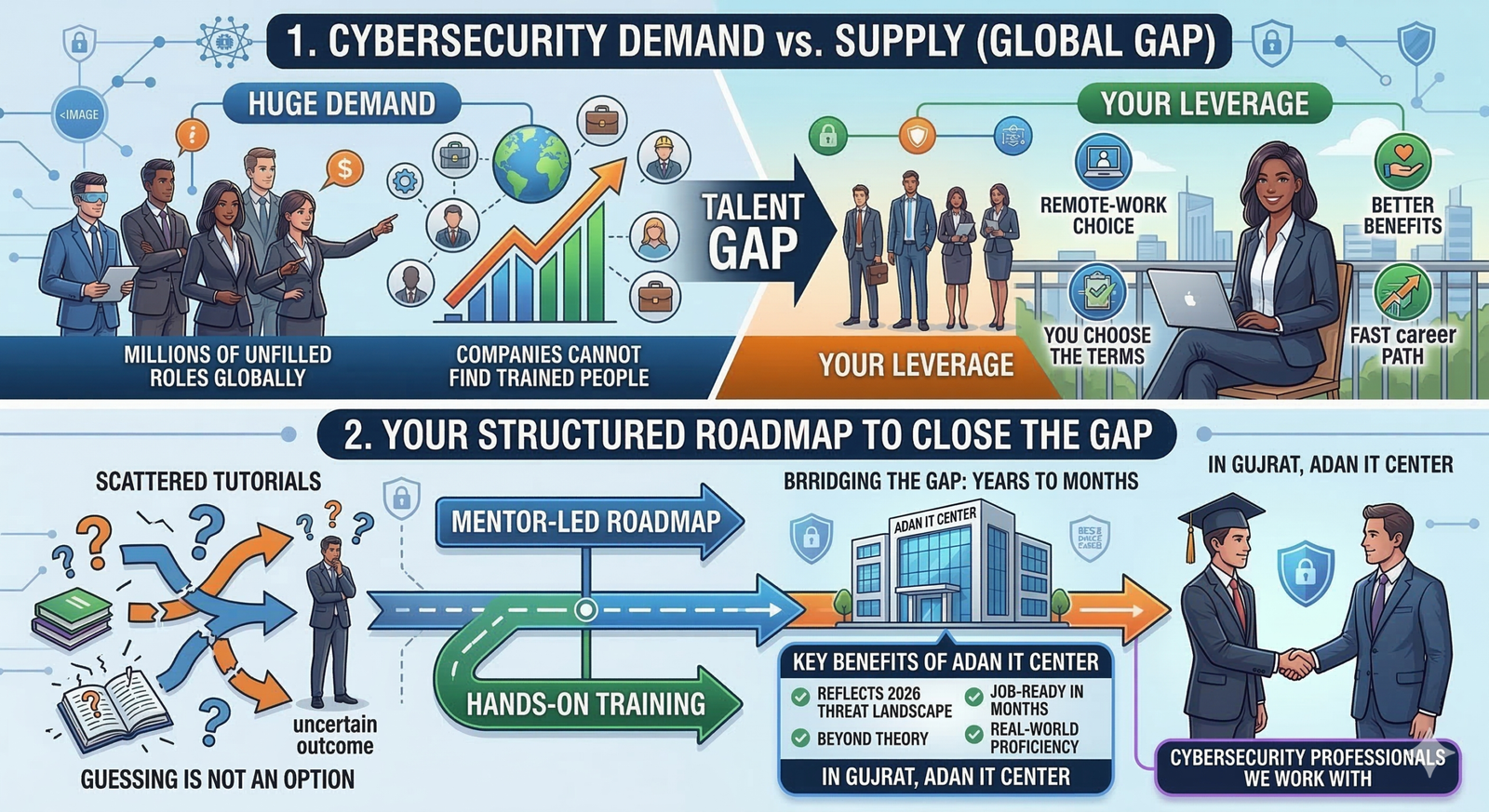
Source: Illustrated by the author showing Bridging the Gap by ADAN IT Centre
The institute emphasizes hands-on learning and real-world application rather than purely theoretical teaching. Its structured approach divides learning into clear phases, making complex concepts easier to grasp.
Cybersecurity Courses Offered
Under its cybersecurity track, it offers multiple courses:
- Introduction to Cybersecurity: It is designed for beginners and gives you ample basic knowledge in 3 weeks.
- Junior Cybersecurity Analyst (CCST): A comprehensive program for building practical security skills. It consists of five courses.
-
Cisco CyberOps Associate: Focuses on real-world security operations and monitoring. It has an 8-week duration.
- Certified Ethical Hacker (CEH). It is an advanced-level course that offers two certification paths and lasts 10 weeks.
- Network Security Professional: It is also a comprehensive, advanced course. It consists of a 12-week duration.
To give you an idea of the landscape you are entering, look at the demand versus the current talent pool:
| Skill Area | Market Demand | Average Entry Salary (2026) |
| Cloud Security | Critical | $95,000 — $110,000 |
| AI/ML Security | Explosive | $105,000 — $130,000 |
| Incident Response | High | $85,000 — $100,000 |
| Ethical Hacking | High | $90,000 — $115,000 |
Table 2: Data from 2026 industry reports. Sources include the Robert Half Salary Guide, BLS projections, and CyberSeek market analysis.
Pro Tip: When looking at this chart, pay attention to the “Superpower,” the skill top companies seek on LinkedIn. Are you drawn to offensive hacking or creating formidable cloud defences? Your decision will shape your next decade.
The ADAN Roadmap: From Student to Professional
Many online ‘How-To’ guides are available, but do they really help or confuse us? Many beginners get stuck in ‘Tutorial Hell.’ They make us watch endless videos without helping us acquire practical skills. ADAN Institute of Technology offers a structured pathway for students, helping them go from scratch to success.
Step 1: Build the Foundation
In the ADAN Cybersecurity Track, you don’t just jump into hacking. You start with the Introduction to Cybersecurity, IT Essentials, and Networking Basics modules.
- Networking Basics: You will learn the OSI model and IP addressing, the core building blocks that keep the internet running.
- Operating Systems: Their curriculum focuses heavily on Linux architecture and file systems. It moves you from Windows to the professional security backbone.
Step 2: Hands-On “Sandboxing”
ADAN moves beyond the classroom through its Practical Labs and Virtualization modules.
- You practice in safe, controlled environments. This allows you to learn without any real risk. You can defend against real-world malware without affecting actual systems.
Step 3: The “Credential” Bridge
Meanwhile, as you build your skills, ADAN prepares you for high-value certifications.
- The program meets PSDA (Punjab Skill Development Authority) standards. It prepares students for Cisco CCNA and CEH ethical hacking certifications.
- Portfolio Building: In addition, during the course, you work on project-based learning. This helps you build work to show recruiters on LinkedIn.
Step 4: The “Mentor Shortcut”
This is the heart of the ADAN experience.
Instead of guessing on YouTube, you receive direct mentorship from active industry professionals. You join a tech hub where you network with peers and experts each day. This can turn a two-year struggle into a six-month career launch.
The most successful professionals don’t succeed alone. They become part of ecosystems, institutions, and communities. These provide access to industry tools, peer networking, and expert mentorship.
This pathway acts as the ‘fast track’, distinguishing dreamers from practitioners. Adan IT Centre offers this very ecosystem, blending industry-grade virtual labs with direct support from active field mentors.
The Strategic Conclusion
As digital technologies shape modern life, it has become more critical than ever to protect information and systems.
This guide on introduction to cybersecurity covers threats, security principles, and key skills. Mastering hands-on skills and ongoing learning are key to building a strong foundation.
For those interested in technology, problem-solving, and digital security, cybersecurity offers a path into a fast-growing field. It’s not just a career. It’s a mission to protect the digital world we rely on every day.
If you love solving problems and wonder how things work, then this Introduction to Cybersecurity is your starting point. Therefore, instead of simply watching the digital world evolve, take the step to protect and defend it.
Pingback: How to Become a Certified Ethical Hacker? - adan3.aitechprojects.net
Pingback: Junior Cybersecurity Analyst -Career Path in 2026 - adan3.aitechprojects.net